 Well, malware has many facets and there is no doubt in that. In
this post, we are going to raise a point about the SpyEye RDP back-connect
plugin and its working. During out talk at Hack
In The Box (HITB) - AMS, we presented about the details of SpyEye
botnet and its ability to work with modular plugins. The RDP plugin in SpyEye
works on the same benchmarks as FTP and SOCKS.
Well, malware has many facets and there is no doubt in that. In
this post, we are going to raise a point about the SpyEye RDP back-connect
plugin and its working. During out talk at Hack
In The Box (HITB) - AMS, we presented about the details of SpyEye
botnet and its ability to work with modular plugins. The RDP plugin in SpyEye
works on the same benchmarks as FTP and SOCKS. Generally, the bot is compiled up with different plugins. The RDP plugin starts a dynamic server on the client machine where the bot is installed. From the victim machine, the bot connects back to main server over RDP. The plugin is well equipped enough to create a hidden user in the victim machine and this account is used to for back server connections. However, this plugin is good enough to allow the remote command server to execute commands on victim machine using RDP.
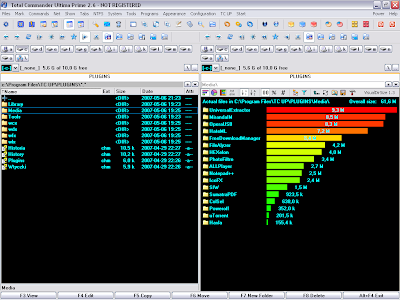
In addition, the SpyEye bot downloads the portable version of from the internet and execute it in the memory on the fly. The beauty of this plugin is that it does not require any system restart when Total Commander is downloaded and installed into the victim machine.
The plugin requires following environmental variables in order to specify the required information for plugin execution
%IP_OF_BC_SERVER%
%PORT_OF_BC_SERVER%
%MAGIC_CODE%
%WINDOWS_LOGIN%
%WINDOWS_PASSWORD%
%URL_TO_PORTABLE_TCMD%
The connection to the bot can be performed using standard Windows tool mstsc.exe Remote Desktop Connection:. It has also been observed that this plugin support only x86 OS and not x64 architectures. In the coming time, hopefully this will be released too.
